If you run some websites/webservices that run over HTTPS, you might be interested in getting some notice before your SSL Certificate is about to expire. If you already use Zabbix, here is a possible way to do so.
Place this script somewhere accessible for the “zabbix” agent-user on the system to monitor:
#!/bin/bash
# checkcert.sh
# 2012, Looke
# Checks whether a SSL x509 Certificate expires within a specified amount of seconds.
# Takes two arguments:
# 1. Certificate
# 2. Time Until Expiration in Seconds
OPENSSL=/usr/bin/openssl
if [ -f "$1" ] && [ "$(file -b $1)" == "PEM certificate" ] && [ -n $2 ] && [ $2 -eq $2 2> /dev/null ]
then
$OPENSSL x509 -noout -checkend $2 -in $1
if [ $? -gt 0 ]
then
echo 1
else
echo 0
fi
fi
Unfortunately there is no way to check the returncode of the command/script in Zabbix, so we have to echo our return value (0 for certificate doesn’t expire within the specified amount of seconds, 1 for certificate does expire).
Also, make sure you have allowed the execution of remote commands in zabbix_agentd.conf:
EnableRemoteCommands=1
Here is how you setup the check in Zabbix:
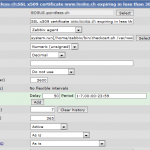
Zabbix Item – Checking if a certificate expires within 30 days (2592000 seconds)
Type: Zabbix agent
Key: system.run[/home/zabbix/bin/checkcert.sh /var/www/www.myvirtualhost.ch/cert/www.myvirtualhost.ch.crt 2592000]
Type of information: Numeric (unsigned)
Data Type: Decimal
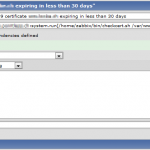
Now, add a Trigger based on this Item and you’re ready to go.
More info
http://www.zabbix.com/documentation/1.8/manual/config/items#zabbix_agent
Good point using openssl to do the dirty work.
I’d rather use a so called user parameter instead of doing remote commands. That way you also can feed the value returned into the zabbix item and create triggers as you like. You might want do some RTFM on user parameters. HTH. :)
Hi Tom,
Thanks for the hint. I will give it a try and do some RTFMing :)
Cheers,
Looke